Critical Cisco FMC Vulnerability — CVE-2026-20131: Unauthenticated RCE Actively Exploited by Interlock Ransomware
Executive Summary
Technical Analysis & Threat Landscape
The Vulnerability: Insecure Deserialization → Unauthenticated RCE
The root cause of CVE-2026-20131 is a classic — yet devastatingly impactful — Insecure Deserialization flaw in the Java-based processing pipeline of the FMC's web management interface.
When the FMC receives certain HTTP requests, it deserialises a Java byte stream to reconstruct an object server-side. The vulnerability exists because no integrity validation or type-checking is performed on the incoming byte stream before it is deserialised. An attacker can craft a malicious serialised Java object (a "gadget chain") that, upon deserialisation by the server, triggers arbitrary code execution within the JVM process context.
Key Technical Characteristics
The fileless execution technique is particularly noteworthy. By executing the malicious Java payload entirely within JVM memory, the threat actor bypasses file-system-based detection, making this one of the more forensically evasive exploitation patterns observed in network infrastructure attacks to date.
Real-World Exploitation: Interlock Ransomware Group
The Interlock Ransomware Group — a financially motivated threat actor known for targeting critical infrastructure and enterprise network perimeters — has been confirmed as the primary exploiter of CVE-2026-20131 during its zero-day window.
Observed Attack Chain (TTPs)
The use of ConnectWise ScreenConnect as a persistence mechanism is a hallmark of sophisticated threat actors blending into legitimate administrative traffic. Its presence on a Cisco FMC device — which has no operational reason to run remote desktop software — is an unambiguous indicator of compromise.
Amazon Threat Intelligence identified this activity using the MadPot global sensor network — a honeypot infrastructure that detected Interlock's exploitation beginning January 26, 2026, predating the public disclosure by 36 days. A misconfigured staging server exposed Interlock's full operational toolkit, giving analysts rare visibility into their complete attack chain, custom RATs, reconnaissance scripts, and evasion methods.
Technical Indicators & Proof-of-Concept (PoC)
Confirmed Indicators of Compromise (IoCs)
Detection Signals
Behavioural Indicators
The following behavioural patterns can be detected without relying on file hashes — critical given Interlock's per-target artifact customization technique:
- Unexpected outbound HTTP PUT requests originating from the FMC appliance to external IP addresses
- Presence of ScreenConnect binaries or service entries on the FMC filesystem
- Anomalous JVM process spawning from the FMC web service process (e.g., child processes of
httpdor the FMC Java service) - PowerShell scripts staging compressed data to network shares using hostname-based directory structures (
\\HOST\Temp\hostname.zip) - HAProxy installations with cron jobs deleting all logs under
/var/logevery 5 minutes - Java ServletRequestListener registrations appearing in web application contexts
- Outbound TCP connections to port 45588 from any internal server
- WebSocket traffic (WS/WSS) originating from FMC or managed devices to unknown external hosts
Log Monitoring — Suspicious FMC Web Access Log Pattern
# Pattern to hunt in FMC access logs (/var/log/httpd/access_log)
# Flag: HTTP PUT to management API endpoints from external/unexpected source IPs
203.0.113.47 - - [26/Jan/2026:04:12:38 +0000] "PUT /api/fmc_config/v1/domain/{domainUUID}/policy/accesspolicies HTTP/1.1" 200 -
# ALERT: Outbound connection FROM FMC to external IP — should never occur in normal operation
SRC=FMC_MGMT_IP DST=EXTERNAL_IP PROTO=TCP DPT=443Conceptual Exploit Pattern — Malicious Java Deserialization Request
PUT /api/fmc_config/v1/domain/DOMAIN_UUID/policy/accesspolicies HTTP/1.1
Host: FMC_MGMT_IP
Content-Type: application/x-java-serialized-object
Content-Length: payload_length
Accept: application/json
binary Java serialized gadget chain payload
# Gadget chain: AnnotationInvocationHandler -> LazyMap -> InvokerTransformer -> Runtime.exec()
# Result: root-level command execution within the FMC JVM process spaceHost-Based Detection — ScreenConnect & Process Hunting
# Check for ScreenConnect presence on FMC filesystem
find / -name "ScreenConnect*" -o -name "connectwisecontrol*" 2>/dev/null
ps aux | grep -i "screenconnect\|connectwise"
netstat -antp | grep ESTABLISHED | grep -v "cisco\|talos\|sourcefire"
# Threat hunt — RMM tools dropped after web access log modification
find / -name "ScreenConnect*" -o -name "*.msi" -newer /var/log/httpd/access_log 2>/dev/null
# Check for anomalous JVM child processes
ps -ef --forest | grep java
# Review access logs for unexpected PUT requests from non-admin IPs
grep '"PUT' /var/log/httpd/access_log | grep -v "TRUSTED_ADMIN_IP"
# Check for suspicious scheduled tasks or cron jobs
crontab -l
ls -la /etc/cron* /var/spool/cron/Mitigation & Recommendations
1. PATCH — Apply Cisco's Security Update Immediately
This is the only complete remediation. Apply the official Cisco patch for CVE-2026-20131 without delay. Cisco has confirmed no workarounds exist — software update is the only viable fix.
Advisory Reference: cisco-sa-fmc-rce-NKhnULJh
Affected: Cisco Secure Firewall Management Center (on-premise)
Not Affected: Cloud-Delivered FMC (patched automatically by Cisco)
Action: Navigate to Cisco Software Center and download the latest FMC release2. HARDEN — Restrict Management Interface Access
The FMC's web-based management interface must not be internet-facing. Enforce access control at the network layer immediately:
# Permit only known, trusted admin IP ranges to reach FMC management port
access-list MGMT_ACL permit tcp ADMIN_NETWORK WILDCARD host FMC_IP eq 443
access-list MGMT_ACL deny ip any host FMC_IP
- Isolate the FMC management interface on a dedicated, non-routable management VLAN
- Enforce MFA on all FMC administrative accounts
- Disable any unused API endpoints or management protocols on the FMC
- Review all FMC user accounts and remove any that are unnecessary
3. MONITOR & HUNT — Assume Breach, Investigate Retroactively
Given the 36-day zero-day exploitation window, treat all unpatched FMC instances as potentially compromised and conduct a thorough threat hunt before declaring the environment clean:
# STEP 1: Check for ScreenConnect or unexpected RMM tools
find / -name "ScreenConnect*" -o -name "*.msi" -newer /var/log/httpd/access_log 2>/dev/null
# STEP 2: Audit outbound connections from FMC (should be near-zero)
netstat -antp | grep ESTABLISHED
# STEP 3: Review access logs for unexpected PUT requests
grep '"PUT' /var/log/httpd/access_log | grep -v "TRUSTED_ADMIN_IP"
# STEP 4: Check for suspicious scheduled tasks or cron jobs
crontab -l
ls -la /etc/cron* /var/spool/cron/
- Review firewall logs for any outbound traffic originating from the FMC management IP
- Engage Incident Response if ScreenConnect artefacts, unknown processes, or outbound FMC connections are identified
- Preserve forensic evidence — take memory images of suspected FMC appliances before remediation, given the fileless execution nature of this exploit
- Monitor for TCP/45588 outbound connections from all internal servers — confirmed post-exploitation indicator
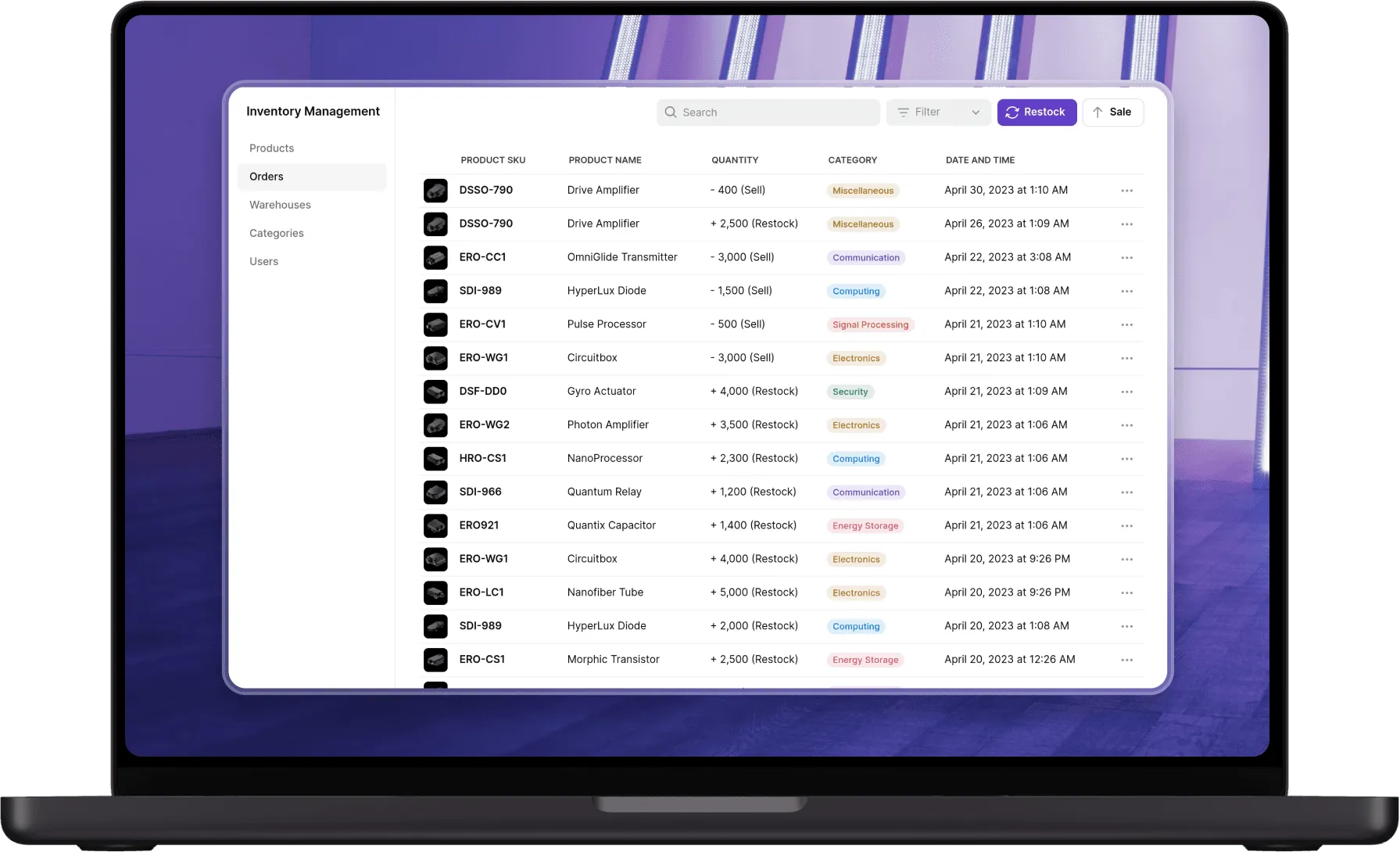
Affected Versions & Patch Status
Conclusion
CVE-2026-20131 is not a vulnerability that can be deprioritised or scheduled for the next maintenance window. A CVSS 10.0, zero authentication required, root-level RCE on a device that controls your entire firewall estate — exploited in silence for 36 days before any patch existed — represents one of the most severe exposure scenarios a network security team can face.
What makes this campaign particularly instructive is how Interlock operated once inside. They didn't just encrypt and ransom immediately. They mapped the network systematically, deployed redundant backdoors in two programming languages, set up proxy relay nodes that wiped their own logs every five minutes, and abused legitimate tools like ScreenConnect and Certify to blend into normal administrative traffic. This is the behaviour of a disciplined, operationally mature threat actor — not an opportunistic script.
The broader lesson is one the industry keeps relearning: perimeter security devices are not immune to the vulnerabilities they are designed to protect against. An FMC compromise doesn't just expose one server — it hands the attacker the master controls for your entire network security policy. That asymmetry is precisely why these devices are targeted first.
Three actions define whether your organisation is exposed or resilient right now:
- If you haven't patched — patch today. There is no workaround. Cisco has confirmed it.
- If you patched after January 26, 2026 — assume potential compromise and hunt using the IoCs in this post before declaring the environment clean.
- If your FMC management interface is reachable from the internet in any way — isolate it immediately, regardless of patch status.
The window between exploitation and detection is where ransomware groups win. Don't give Interlock that window.
References
.svg)










.svg)